As we all may know Microsoft is still busy migrating all Intune tenants to the new Azure infrastructure, a hell of a job if you ask me!
If you are migrated you are able to use the new Mobile Application Management policies or also called App Protection policies, to manage your apps on devices that are managed by Intune or are not managed by Intune, also known as MAM without enrollment. In this blog I would like to point out the options for iOS and Android that are currently available in the new Intune portal on Azure.
Defining MAM App Protection Policies
One of the first steps is creating a App Protection Policy that you can target to Applications and groups of users. These App Protection Policies are available for iOS, Android and Windows.
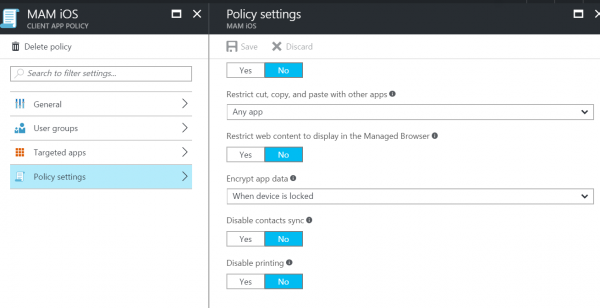
For Android and iOS we can control settings like listed below:
| Setting | Available on |
| Prevent iTunes and iCloud backups | iOS |
| Prevent Android backups | Android |
| Allow app to transfer data to other apps | iOS and Android |
| Allow app to receive data from other apps | iOS and Android |
| Prevent “Save As” | iOS and Android |
| Restrict cut, copy, and paste with other apps | iOS and Android |
| Restrict web content to display in the Managed Browser | iOS and Android |
| Encrypt app data | iOS and Android |
| Disable contacts sync | iOS and Android |
| Disable printing | iOS and Android |
| Require PIN for access | iOS and Android |
| Require corporate credentials for access | iOS and Android |
| Block managed apps from running on jailbroken or rooted devices | iOS and Android |
| Recheck the access requirements after (minutes) | iOS and Android |
| Offline interval (days) before app data is wiped | iOS and Android |
| Block screen capture and Android Assistant | Android |
The Windows policies however, are using the Windows Information Protection feature, which is available since the Windows 10 anniversary update. More on Windows Information Protection in a later blog.
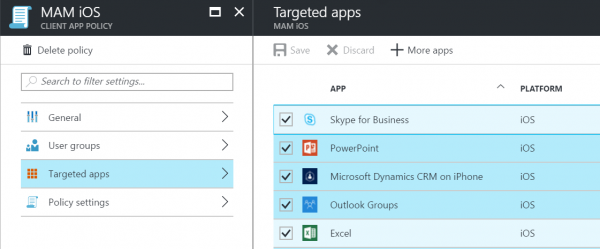
So when you configure an Application Protection Policy we need to target it to a group of users and to the Apps you want to use the Application Protection Policy (MAM) for.
After this is configured we need to deploy assign the apps to the users..
Deploying Assigning Apps
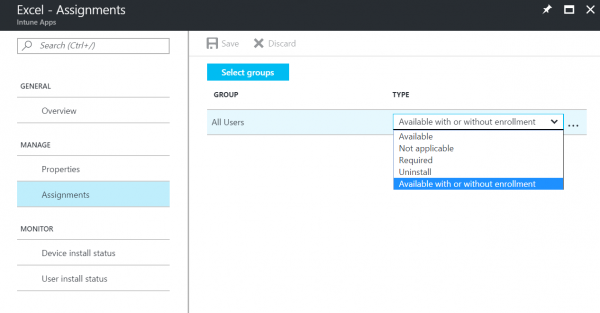
First of all, we are not deploying apps anymore.. After doing this for ages in Configuration Manager and Intune we are now talking about assigning apps to groups of users or devices. Reason for this is that the common way to deploy anything in the new Azure Portal is assigning it… 😉
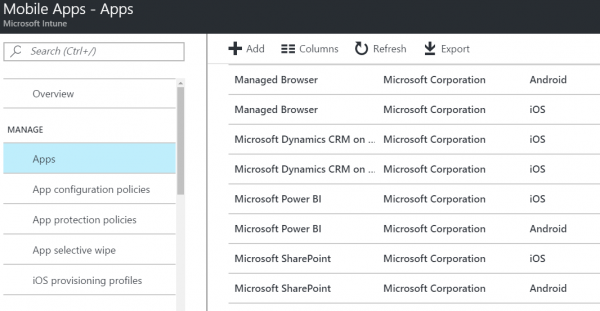
When you access the new Intune portal on Azure (https://portal.azure.com) you can access the applications via Microsoft Intune >> Mobile Apps. There you find a list of prepopulated applications of Microsoft that have the Intune SDK integrated and support the App Protection Policies, which saves you lots of time creating those apps yourself.
Apps needs to be assigned to a group of users, you can assign the app as follows;
| Assignment | Description |
| Available | App will be available in the Company Portal |
| Not applicable | The app is not installed and not shown in the Company Portal for a specific group |
| Required | App will be pushed to all members in the group |
| Uninstall | App will be uninstalled from all member in the group |
| Available with or without enrollment | The App is available for the MDM managed device and the not managed device |
So I do not want to support MAM without Enrollment
If you do not want to support MAM without enrollment, you need to enable the Conditional Access policies for the services that you want to enforce enrollment. So for instance if you do not want to allow Outlook being used on devices that are not managed to access your email, you need to configure Conditional Access for Exchange Online.
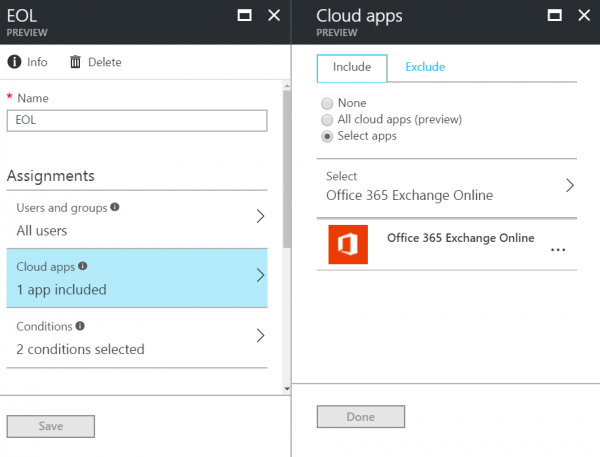
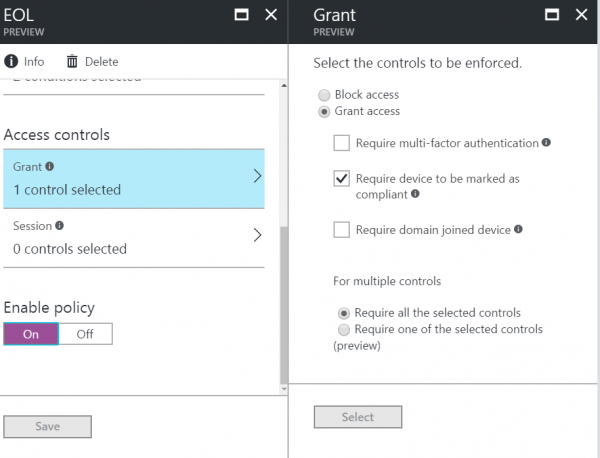
So when a device is enrolled and marked as compliant, access to Exchange Online is allowed. This counts for instance also for other Office 365 services or other apps in Azure AD.
Note:
Currently for MSI via MDM apps or Line of Business Apps (APK, IPA files) still need to be deployed via the Silverlight console. When this changes or other changes to the Preview portal of Intune are made, I will change this blog or refer to a new blog here.
(updated 1st May 2017) Just days after releasing this blog Microsoft updated the Intune on Azure service and added the ability to upload the Android and Apple LOB apps and Windows Mobile MSI apps. See the new blog here!
Till next time!


